Protect your business and what’s important
Cybersecurity
Outsourcing your cybersecurity needs
Cybersecurity is more critical than ever, with businesses facing constant threats from hackers, data breaches, and cyberattacks. Managing security in-house requires specialized expertise, continuous monitoring, and staying ahead of evolving threats—a challenge for many organizations. Instead of taking on the risk alone, outsourcing cybersecurity allows you to protect your business with expert solutions tailored to your specific needs. From vulnerability assessments to threat detection and incident response, cybersecurity professionals ensure your data, systems, and customer information remain secure.
By partnering with experienced security experts, you gain proactive protection against cyber threats without the burden of hiring and maintaining an in-house team. Professionals implement the latest security measures, monitor for suspicious activity, and respond swiftly to potential breaches, minimizing risks and downtime. Whether you need network security, cloud protection, compliance support, or penetration testing, outsourcing cybersecurity ensures you stay ahead of cyber threats while focusing on growing your business with confidence.
How To Take Screenshots on macOS
There are many reasons why you would want to take screenshots on macOS of your computer. Maybe you are trying to capture a web page or an application window. Whatever the reason, taking a screenshot is one of the most valuable things you can do. Luckily, it's not hard...
Best Times to Post on Tiktok
Having a good understanding of when the best times to post on Tiktok is essential to get more engagement. You can do this by monitoring your audience's activity on the platform. Once you have an idea of what the algorithm prefers, you can make your own posts during...
Unlock the Secret to See Instagram Stories Anonymously
Viewing Instagram stories anonymously can be a bit tricky as Instagram does not provide a built-in feature for this. However, there are several third-party services and workarounds that claim to allow users to view Instagram stories without the poster knowing. Please...
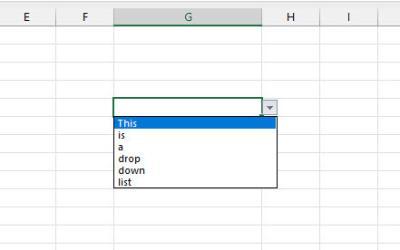
How to Create a Drop Down List in Excel
If you are new to Excel, you will want to know how to create a dropdown list in your spreadsheet. There are a couple of ways to do this. You can create your own by hand, or you can use a template. Whatever you choose, make sure you are following the rules and...
How To See Who Viewed My Instagram
If you want to know who is viewing your Instagram posts, you have come to the right place. In this article, you'll discover some of the best tools you can use to find out more. These include Analyzer Plus, SocialView for Instagram, and Follower Analyzer. You'll also...
How Can I Make Money From My Website?
So you are deciding to start a business online. You have your domain and you are just choosing your hosting. But what is the next step? How can you go on to make money from your website, rather than just have an information page that sits on the internet but doesn’t generate any revenue? Have a look at these simple suggestions to help get you started.